CVE Detection / Monitoring with NinjaOne Custom Fields
This post will hold detection scripts for any serious CVE vulnerability that we write detection scripts for in the future. It will be updated and added to as new vulnerability detection scripts are written.
CVE-2022-41099
This script has been compiled using information from the following Microsoft sources:
This article relates to CVE-2022-41099 which is a vulnerability in the Windows Recovery Environment (WinRE) which could allow a successful attacker to bypass the BitLocker Device Encryption feature on the system storage device. An attacker with physical access to the target could exploit this vulnerability to gain access to encrypted data.
:::bug Fixed a Bug
Thanks to DTGBilly from the NinjaOne Users Discord for pointing out that in altogether far too many places I had typo'd the CVE as CVE-4022-41099 instead of CVE-2022-41099 🤦♂️ this included field names and labels so please check yours are correct as now shown in the post.
:::
:::note Parameters!
Since version 1.2.0 (2023-03-21) this script now requires one of two mandatory parameters.
-
If you are checking for the presence of the small "Safe OS Dynamic Update (SODU)" which is the minimum required change to mitigate the vulnerability use the
-CheckPackageparameter and if required alter the-MountDirectoryand-LogDirectoryparameters (defaults toC:\RMM\WinRE). -
If you are checking for the presence of the larger "Servicing Stack Update (SSU)" or "Dynamic Cumulative Update" which updates more than is required to mitigate the vulnerability, but may offer other benefits including new WinRE functionality or more reliable reset/restore behaviours use the
-CheckImageparameter which checks the image build version.
If you were passing these in NinjaOne your parameter preset might look like this:
-CheckPackage -MountDirectory C:\RMM\WinRE -LogDirectory C:\RMM\WinRE
or this:
-CheckImage
:::
:::bug Windows Recovery Environment (WinRE) Not Enabled
Before version 1.3.0 the script did not check if WinRE was enabled which could lead to confusing error output in the event WinRE was disabled. Now if you get the WinRE not enabled warning you are clear on why the script isn't executing.
A simple reagentc /enable should enable WinRE or at least provide some useful troubleshooting output.
:::
Creating Fields
- Role Custom Fields are custom fields that are specific to a device role.
- Global Custom Fields are custom fields that are applicable to all devices and/or to a location and/or organisation
When you create your custom field you need to make sure that you set the Scripts permission to ensure that you can read or write to the field from your scripts - as appropriate for the script you're using.
We're adding one role custom field for devices with the Windows Desktop or Laptop and Windows Server roles, note that we've customised slightly the autogenerated machine name here, if you use the default adjust the field name in the script appropriately.
| Field Label | Field Name | Field Type | Description |
|---|---|---|---|
| CVE-2022-41099 | CVE202241099 | Checkbox | Whether the device has a WinRE image vulnerable to CVE-2022-41099 |
The Script
This script was updated after being published, if you're using it please compare the version you have with the version available here.
This script was last updated on 2023/04/13.
loading...
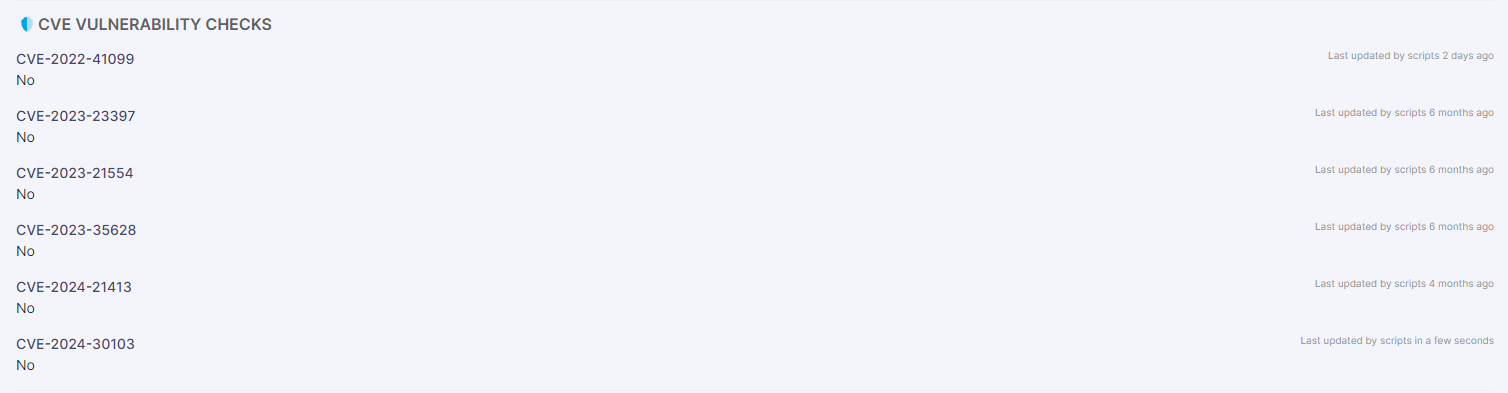
The Results
We run this script daily and have a corresponding monitor setup to check CVE fields with a value of "Yes" and alert us if any are found. You'll find information on remediating this vulnerability in this followup post.
CVE-2023-23397
This script has been compiled using information from the following Microsoft sources:
- Release notes for Microsoft Office security updates
- Update history for Microsoft 365 Apps (by date)
- Update history for Office Beta Channel
Thanks to:
- Concentus on the NinjaOne Users Discord for helping me run down and test different versions of Office to ensure this script was as accurate as possible.
- Wisecompany on the One Man Band MSP Discord for reminding me to add an exit code and not overuse
Write-Warning! - Thanks to KennyW on the MSPGeek Discord for helping find an error where certain versions were incorrectly detected as not vulnerable!
- Thanks to Alkerayn on the NinjaOne Users Discord for helping find an error where certain channels were incorrectly detected as not vulnerable and identifying that we needed to first check the GPO-configured update channel!
- Thanks to Tanner - MO on the MSPs R Us Discord for pointing out that version comparisons should all use
-ltinstead of-neto ensure future compatibility / accuracy. - Thanks to DarrenWhite99 on the MSPGeek Discord for pointing out that the check for the GPO UpdateChannel was completely nonsensical and incompletely written.
- Thanks to JSanz on the NinjaOne Users Discord for pointing out the GUID matching issue/bug.
- Thanks to Jhn - TS on the NinjaOne Users Discord for discovering the issue with empty registry props causing the script to error.
This has only been tested against M365 Apps and Office 2021 VL versions "en masse" and only 64-bit office - if it doesn't work for you let me know on the NinjaOne Users Discord and I'll see what I can do to fix it!
This article relates to CVE-2023-23397 which is a vulnerability in Microsoft Outlook whereby an attacker could access a user's Net-NTLMv2 hash which could be used as a basis of an NTLM Relay attack against another service to authenticate as the user.
Creating Fields
- Role Custom Fields are custom fields that are specific to a device role.
- Global Custom Fields are custom fields that are applicable to all devices and/or to a location and/or organisation
When you create your custom field you need to make sure that you set the Scripts permission to ensure that you can read or write to the field from your scripts - as appropriate for the script you're using.
We're adding one role custom field for devices with the Windows Desktop or Laptop role, note that we've customised slightly the autogenerated machine name here, if you use the default adjust the field name in the script appropriately.
| Field Label | Field Name | Field Type | Description |
|---|---|---|---|
| CVE-2023-23397 | CVE202323397 | Checkbox | Whether the device has an Office or Microsoft 365 Apps version vulnerable to CVE-2023-23397. |
The Script
This script was updated after being published, if you're using it please compare the version you have with the version available here.
This script was last updated on 2023/04/13.
loading...
The Results

We run this script daily and have a corresponding monitor setup to check CVE fields with a value of "Yes" and alert us if any are found. To remediate this vulnerability update Microsoft Office by running something like this:
This script was updated after being published, if you're using it please compare the version you have with the version available here.
This script was last updated on 2023/03/16.
loading...
This update script will force restart Office apps - it should restore open files automatically but if you want a softer approach replace the Start-Process line with:
Start-Process -FilePath $C2RPath -ArgumentList '/update user forceappshutdown=true updatepromptuser=true' -Wait
Prejay on the MSPGeek Discord has helpfully suggested the following to update C2R Office builds without a user logged in or as system:
Start-Process -FilePath $C2RPath -ArgumentList '/frequentupdate SCHEDULEDTASK displaylevel=false' -Wait
Mark Hodges (also on the MSPGeek Discord) has also helpfully suggested this more comprehensive update script which will update Office 2016 and 2019 as well as C2R Office.
CVE-2023-21554
This script has been compiled using information from the following Microsoft sources:
This article relates to CVE-2023-21554 which is a vulnerability in the Microsoft Message Queuing system which could allow remote code execution.
Creating Fields
- Role Custom Fields are custom fields that are specific to a device role.
- Global Custom Fields are custom fields that are applicable to all devices and/or to a location and/or organisation
When you create your custom field you need to make sure that you set the Scripts permission to ensure that you can read or write to the field from your scripts - as appropriate for the script you're using.
We're adding one role custom field for devices with the Windows Desktop or Laptop role, note that we've customised slightly the autogenerated machine name here, if you use the default adjust the field name in the script appropriately.
| Field Label | Field Name | Field Type | Description |
|---|---|---|---|
| CVE-2023-21554 | CVE202321554 | Checkbox | Whether the device has the MSMQ features installed and is missing the April 2023 Security Update. |
The Script
This script was updated after being published, if you're using it please compare the version you have with the version available here.
This script was last updated on 2023/03/16.
loading...
The Results
We run this script daily and have a corresponding monitor setup to check CVE fields with a value of "Yes" and alert us if any are found. To remediate install the April 2023 Security Update.
CVE-2023-35628
This script has been compiled using information from the following Microsoft sources:
This article relates to CVE-2023-35628 which is a vulnerability affecting Microsoft Outlook's email rendering system which could allow remote code execution.
Creating Fields
- Role Custom Fields are custom fields that are specific to a device role.
- Global Custom Fields are custom fields that are applicable to all devices and/or to a location and/or organisation
When you create your custom field you need to make sure that you set the Scripts permission to ensure that you can read or write to the field from your scripts - as appropriate for the script you're using.
We're adding one role custom field for devices with the Windows Desktop or Laptop and/or Windows Server role, note that we've customised slightly the autogenerated machine name here, if you use the default adjust the field name in the script appropriately.
Thanks to Gavsto for stopping me doing down the rabbit hole of checking KB numbers by pointing out that it wouldn't be future proof once the next cumulative update was released!
| Field Label | Field Name | Field Type | Description |
|---|---|---|---|
| CVE-2023-35628 | CVE202335628 | Checkbox | Whether the device is updated/patched for CVE-2023-35628. |
The Script
loading...
The Results
We run this script daily and have a corresponding monitor setup to check CVE fields with a value of "Yes" and alert us if any are found. To remediate install the December 2023 Cumulative Update.
CVE-2024-21413
This script was updated after being published, if you're using it please compare the version you have with the version available here.
This script was last updated on 2023/02/16.
This script has been compiled using information from the following Microsoft sources:
This article relates to CVE-2023-35628 which is a vulnerability affecting Microsoft Outlook's preview pane system which could allow remote code execution.
The updates include changes/corrections to the targetted versions - check your version please!
Creating Fields
- Role Custom Fields are custom fields that are specific to a device role.
- Global Custom Fields are custom fields that are applicable to all devices and/or to a location and/or organisation
When you create your custom field you need to make sure that you set the Scripts permission to ensure that you can read or write to the field from your scripts - as appropriate for the script you're using.
We're adding one role custom field for devices with the Windows Desktop or Laptop and/or Windows Server role, note that we've customised slightly the autogenerated machine name here, if you use the default adjust the field name in the script appropriately.
| Field Label | Field Name | Field Type | Description |
|---|---|---|---|
| CVE-2024-21413 | CVE202421413 | Checkbox | Whether the device is updated/patched for CVE-2024-21413. |
The Script
loading...
The Results
We run this script daily and have a corresponding monitor setup to check CVE fields with a value of "Yes" and alert us if any are found. To remediate install the applicable Office / M365 Apps February 2024 Security Update.
CVE-2024-30103
This script has been compiled using information from the following Microsoft sources:
This script also uses information from the following non-Microsoft sources:
Thanks to:
- Xzul on the NinjaOne Users Discord for bringing this one to the forefront of my attention as I'd seen it and then promptly forgotten about it!
This article relates to CVE-2024-30103 which is a vulnerability affecting Microsoft Outlook's email rendering system which could allow remote code execution.
Creating Fields
- Role Custom Fields are custom fields that are specific to a device role.
- Global Custom Fields are custom fields that are applicable to all devices and/or to a location and/or organisation
When you create your custom field you need to make sure that you set the Scripts permission to ensure that you can read or write to the field from your scripts - as appropriate for the script you're using.
We're adding one role custom field for devices with the Windows Desktop or Laptop and/or Windows Server role, note that we've customised slightly the autogenerated machine name here, if you use the default adjust the field name in the script appropriately.
| Field Label | Field Name | Field Type | Description |
|---|---|---|---|
| CVE-2024-30103 | CVE202430103 | Checkbox | Whether the device is updated/patched for CVE-2024-30103. |
The Script
loading...
The Results
We run this script daily and have a corresponding monitor setup to check CVE fields with a value of "Yes" and alert us if any are found. To remediate install the applicable Office / M365 Apps June 2024 Security Update.